GitHub OAuth
Creating a custom GitHub OAuth application
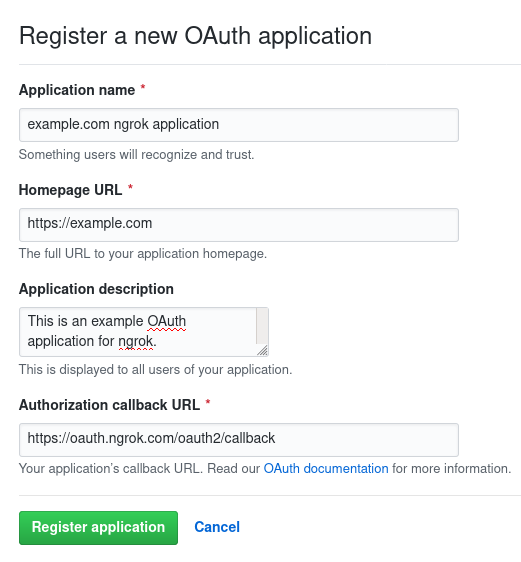
- Follow GitHub's documentation until the final step of submitting the registration form.
- Set the Authorization callback URL to
https://idp.ngrok.com/oauth2/callback. - Submit the form. A working example registration:
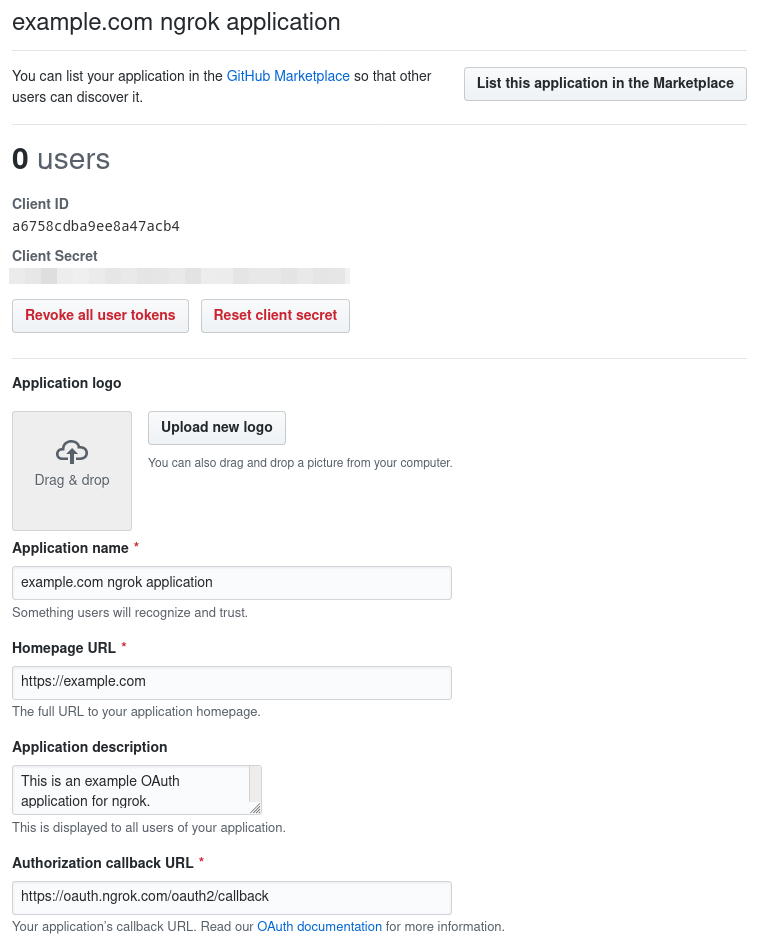
- Save the client ID and client secret from the application overview:
Update your ngrok endpoint traffic policy
- Access the ngrok Dashboard Endpoints page and locate an existing endpoint you'd like to add this to or create a new one.
- In your traffic policy, add the following configuration:
Loading…
- Click Save to validate and update your traffic policy.
Configure access control
Optionally, configure access control to your service by only allowing specific users or domains. For example:
Loading…
Known Limitations
- Users who utilize GitHub's private email setting are not able to sign in.