Organizations and enterprises must ensure robust security for their endpoints without causing any interruptions to their developers’ experience and productivity. This guide describes the best practices and features organizations can apply to consistently secure developers using ngrok.Documentation Index
Fetch the complete documentation index at: https://ngrok.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
The “Front Door” method
Instead of exposing individual developer endpoints publicly, you can implement a more secure approach: Creating a single, centralized Cloud Endpoint managed by security teams. This endpoint can be customized with Traffic Policies while keeping developer endpoints private and protected.Architectural reference
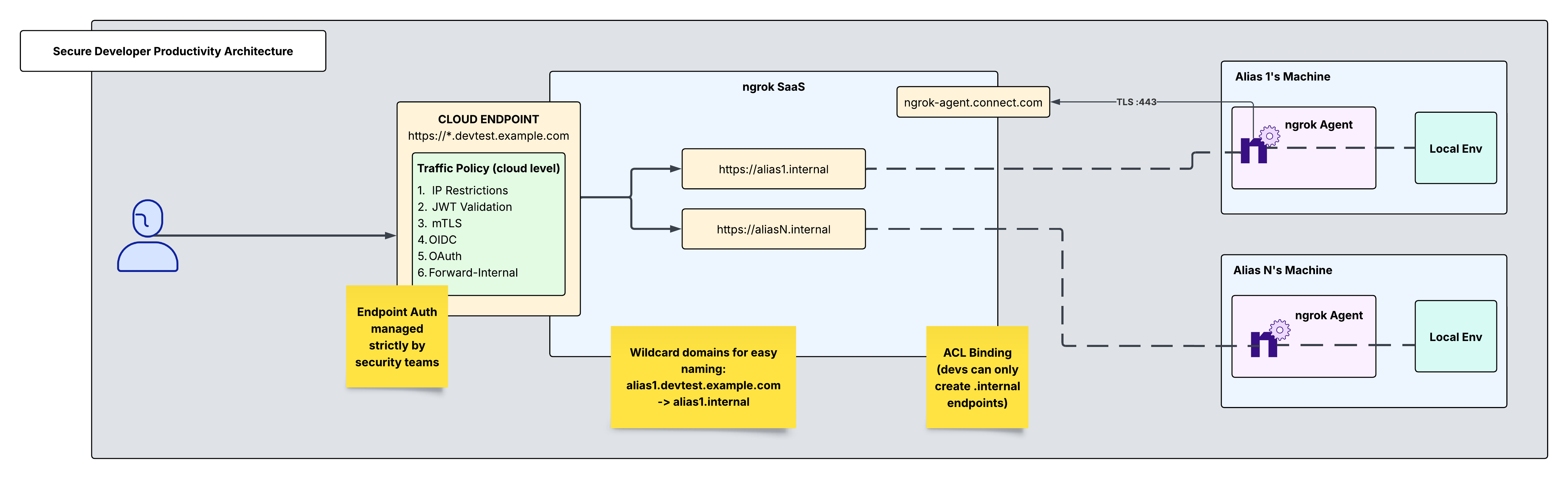
- Cloud endpoint Traffic Policies
- Authtokens and ACL restrictions
- Users and access control
Add developers as team members to your ngrok account
This will allow you to add each developer using ngrok to your central ngrok account. With RBAC (available on ngrok’s pay-as-you-go plan), you also have the option to restrict their access to read-only.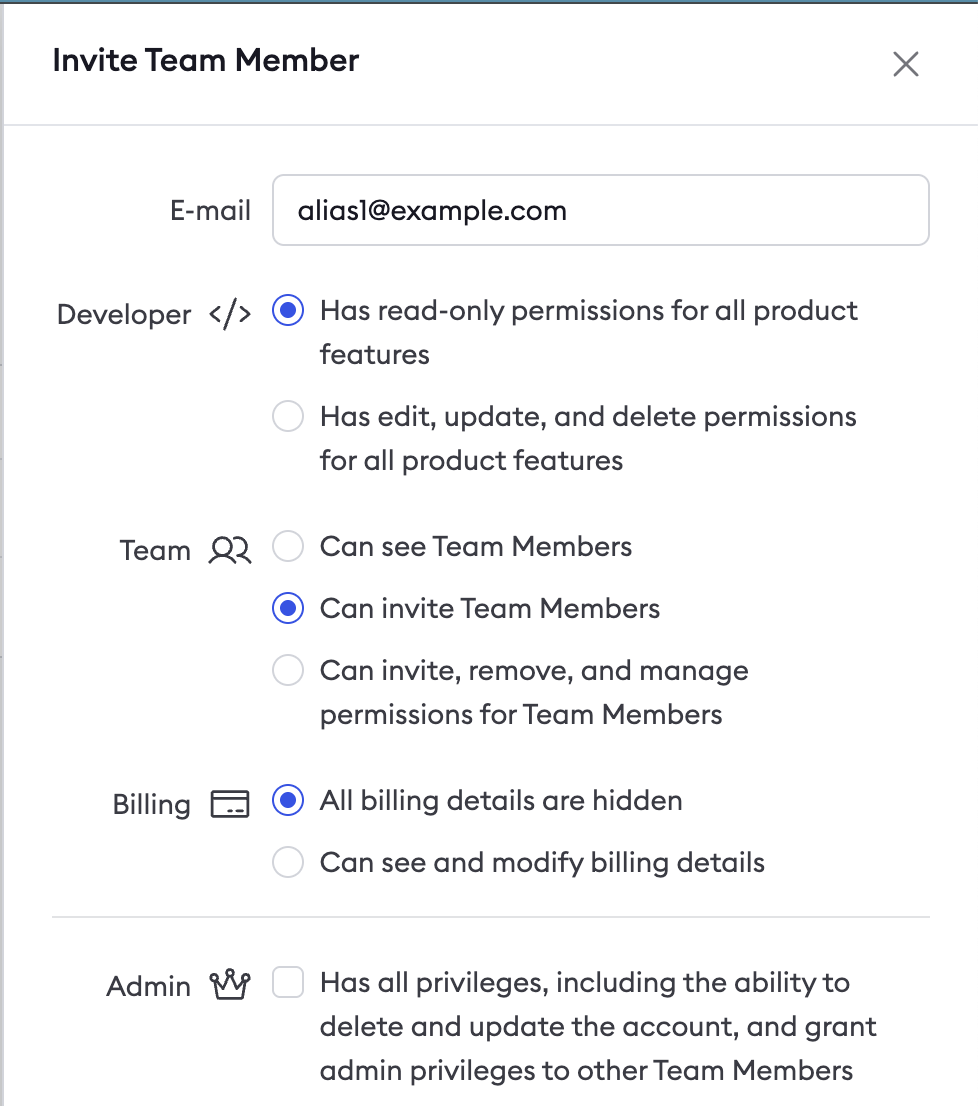
Create an authtoken for each developer
Create a tunnel authtoken for each developer. This authtoken will be specific to each user and will be their key to setting up internal endpoints. Next, assign it an ACL rule. By assigning an ACL rule, you can ensure that this user with this authtoken may only create one internal endpoint bound to their alias. Navigate to the authtokens section on your dashboard and click “new authtoken” and set the description, set the owner to the developer email, and assign it an ACL rule as shown below: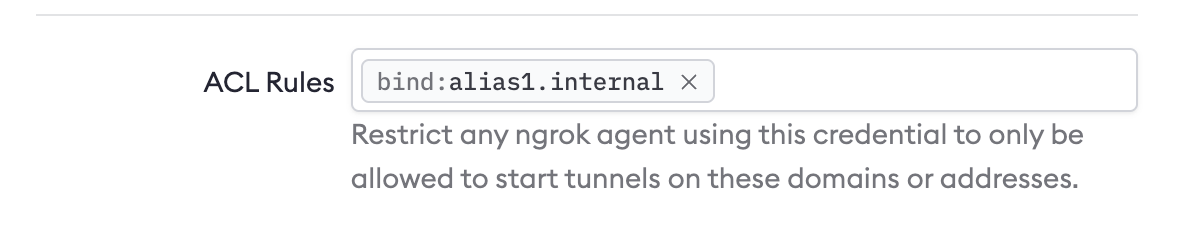
Developer installs ngrok Agent and defines an internal endpoint in ngrok.yml
Have the developer install the ngrok agent and then have them run the command below to ensure their agent uses the proper authtoken you provisioned for them in the previous step.- End with the .internal domain extension
- Use the internal binding
/path/to/ngrok/ngrok.yml. Have the developer add their internal endpoint in their configuration file. The final config file should look like this:
Reserve a domain for your wildcard Cloud Endpoint
Reserving a wildcard domain is the first step in creating a wildcard Cloud Endpoint to receive traffic on any subdomain of your domain. Navigate to the domains section in your dashboard and click “new domain”. Any naming convention you use for this domain will require proper DNS and CNAME records. These targets are returned after domain creation and can take 5-10 mins for ssl to be established. For billing information on wildcard endpoints, see wildcard endpoints pricing.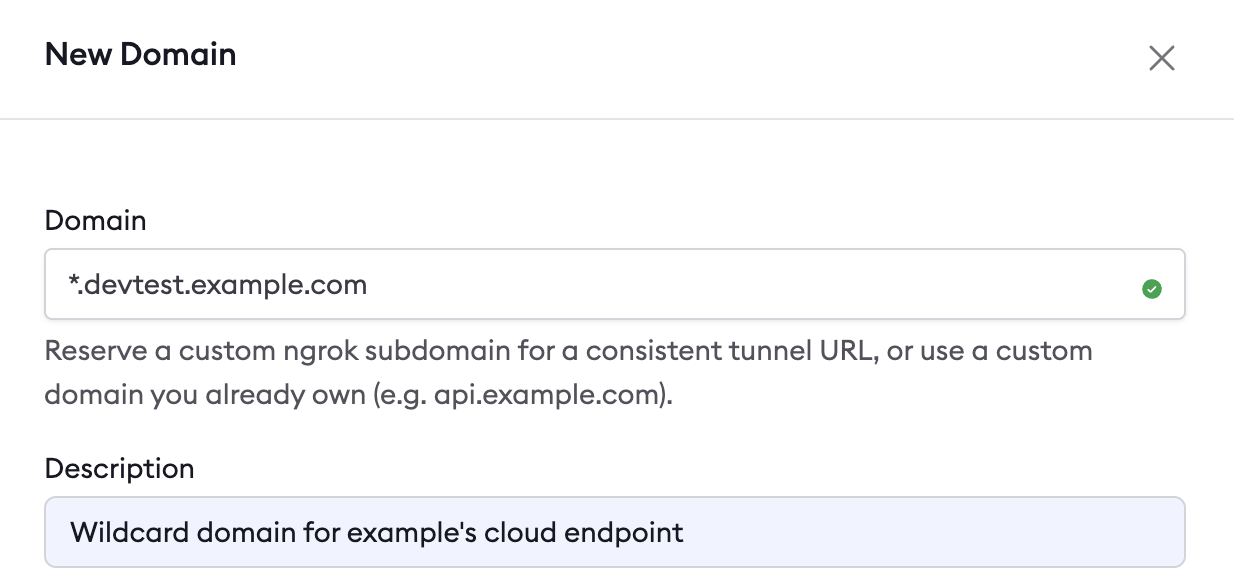
Create a public Cloud Endpoint and Traffic Policy
Cloud Endpoints are persistent, always-on endpoints whose creation, deletion, and configuration are managed centrally via the Dashboard or API. They exist permanently until they are explicitly deleted. Cloud Endpoints do not forward their traffic to an agent by default and instead only use their attached Traffic Policy to handle connections. This Cloud Endpoint will multiplex across several internal endpoints which point to their corresponding local development environments. You can use Traffic Policy to forward traffic from your Cloud Endpoint to the correct internal endpoint based on the hostname of the Cloud Endpoint that developers make requests to. Since the Cloud Endpoint is set up as a wildcard URL, any text placed where the wildcard is will forward to its corresponding internal endpoint.alias1.devtest.example.com → alias1.internal → alias1's local env
So, all alias1 has to do is go to that Cloud Endpoint URL in their browser and they will be able to access their local environment. Same goes for alias2, alias3, and aliasN.
To achieve this dynamic routing, replace the default Traffic Policy on the Cloud Endpoint in the dashboard with the following:
Secure your Cloud Endpoint
Now that traffic is forwarded correctly from the Cloud Endpoint to its corresponding internal endpoints, you can layer on security to the public Cloud Endpoint. There are a variety of Traffic Policy actions to choose from to achieve this. Listed below are YAML snippets and curl commands below for how to enable IP Restrictions, JWT Validation, and mTLS. There are many other actions to choose from which can be found in Traffic Policy Actions. These actions will be added to your existing Traffic Policy config, preceding the forward-internal action.IP restrictions
For developers with a designated source IP, you can use the restrict-ips action to allowlist trusted source IPs where only these IPs will be able to access this Cloud Endpoint.JWT validation
You also have the option to send a JWT to ngrok, specify an allowlist of issuers/JWKS URLs, and ngrok will validate the JWT.mTLS
If you would rather use a CA or PEM version in this scenario, you can also enable mTLS where TLS termination will happen at the ngrok cloud edge.Create a custom connect URL
Custom connect URLs are available with ngrok’s pay-as-you-go plan. This provides a white-labeling capability so that your ngrok agents will connect to connect.example.com instead of the default connection hostname (connect.ngrok-agent.com). Dedicated IPs that are unique for your account which your agents will connect to are also available. This takes away any danger of rogue agents in your network trying to call home and adds an additional layer of security by specializing your ngrok connectivity.Recap
You have now integrated a system that allows your security team to centrally manage and secure a Cloud Endpoint which developers can seamlessly use to access applications running in their local environments. To recap what you’ve built:- One ngrok agent per developer machine - ACL restricted authtokens provisioned by security specialists for developers.
- Local, uninterrupted development and testing for engineers, made securely available via cloud and internal endpoints.
- Granular access with a composable Traffic Policy offering refined and robust security measures for a singular public Cloud Endpoint.